Losing Our brains with disruptive technologies (XX): Big brother is watching.
 Today´s publication is about the activity: Protect, which is a synonym of guard, shield, secure, preserve, defend. What is happening with the technology disruptors when it comes to “protect” activities?
Today´s publication is about the activity: Protect, which is a synonym of guard, shield, secure, preserve, defend. What is happening with the technology disruptors when it comes to “protect” activities?
It is my aim to show you a skim overview of the activities related to the word protect.
When it comes to the function “Protect”, the majority of human beings’ inventions have been driven by this need. Even fire, during the paleolithic era, was used to defend territories from the dangers of other species as animals that wanted them for a “petit dejeuner”. We possess more than 6,000 years of inventions background, related to the word “protect”. I will limit this word to the activities related to shielding of people´s lives which are not related to curing (health context) but to guard against physical harm. That is how the “to protect” activities are defined by their own industry.
These technologies can be classified in:
1. Military technologies: used by official government army forces to keep citizens from harm. Or on the other side, used by terrorists, militias, guerrillas or religious movements anti-status quo forces. These technologies are utilized for war. I also include here, the whole combo of NAIQI technologies adopted by individuals on a case by case basis. Military technologies are employed to protect individuals in a wild and wide range… such as rifles or guns or even the most simple pepper spray.
2. Property security systems technologies: related to those technologies which help to detect and prevent robberies or to detect wrongdoings at a physical tangible level in property such as home, offices, parking lots or offices. Here we can include the whole portfolio of different alternatives (by contract or DIY), all of them include security cameras, integrated software and sensors systems and applications linked to your smartphone or personal computers. At the moment there are multiple specialized corporations which offer these services, for example, in the USA, we can name at ADT systems, Protect America, Front Point, etc. Usually, these companies offer integrated arrangements which incorporate doorbell cameras, wireless security cameras, smart locks, windows and door sensors. The extent of the services may include smart thermostats, fire extinguishers, carbon monoxide detectors, smoke alarms and other family safety devices. For the DIY category, according to an article from Cnet, the most relevant are: Simplisafe Home security, Abode, Nest Secure, Honeywell Smartphone Security System, Scout Alarm, Smart things ADT home security starter kit, etc.
3. City and community Integrated Security Systems: Security systems incorporate technologies that enhance the security and safety in public places, and transit customers in the cities, streets, parks and routes infrastructures. These technologies include radio communications, silent alarms, covert microphones, closed-circuit television cameras (also known as video surveillance), automatic vehicle location (AVL), drones and other equipment that assist municipalities or public agencies in monitoring and responding to situations of irregularities. In addition, all modes of public transportation systems, whether urban or rural, bus, rail, or ferry, can benefit from the implementation of a security system. They can also warn officials of possible intentional acts of crime or violence.
Every single invention in the security or protection domain has at least one or all the combo of NAIQI technologies (Nanotech, Artificial Intelligence, Quantum processing and the Internet of Things and Robotics). From video surveillance, alarms, circuit television to the weapons, artillery, and transportation utilized for military purposes. During the last 20 years the most relevant protection inventions have been: autonomous robot vehicles to be used in battlefields, plenty of prototype robots that may be used instead of soldiers, landmine destroyers, tiny camera chips, invisible technology for optical camouflage, fire protection fluids, nanowires capable of tiny nano-engines used for military purposes, electromagnetic pulse guns to provoke maximum pain, laser rifles, helicopter laser, rifle firing electric bullets, solar power and electric tanks, BEAR battlefield extraction assist robots, Mships, water harvesting machines, any type of autonomous auto with-solar power for wars, military drones, led incapacitors, reconnaissance devices, raytheon active protection systems, orbital internet, quantum computers, bionic contact lens for recognition of temperature in the battlegrounds, fabrics to protect the skin when in war, invisibility materials, internet of things applied to every single military device you can imagine, smart bullets XM25, high speed airplanes used for military purposes, Georgia Tech airconflict and escape robot, 3D printers used to produce military manufacturing parts, smart rockets with nanosensors, IMX explosives, XFLex Blast protection, Raytheon XOS Iron man suits for specialized military purposes, surveillance hummingbirds, high beta fusion reactor, smart sensors to be utilized in every single military or protection activity, security video cameras for cities, countries and homes, safety transparent trucks, people trackers, safeguard systems and applications to be monitored using smartphones, VR wearable lens military uses, location trackers, etc… etcétera, etcétera, etcétera.
Outstanding issues or vulnerabilities related to protection technologies:
Cybersecurity: When it comes to our inventions related to protection, cybersecurity is the most relevant one. Any hacker can get into your home, IoT or government computers. The internet is tied to hacking. Anyone can access your passwords or ID or any type of device recognition strategies, and the same security systems may be used against yourself by those who wish to harm you. The Internet and the Internet of things is not a safe place, and will never be.
Privacy Issues: We need to review the strategic path of protection technologies, not because they are wrong… but because privacy is compromised. If in our quest for security, we have forgotten that individuals must defend their own privacy at all costs. If by using these security systems, our privacy is jeopardized or discredited, it is also destroying our own right to be retreated from the rest, particularly when our most basic actions will be handled or mismanaged against us. Human beings can´t lose their own right to privacy.
Identifiers for IoT are not unique yet. Even though “Silicon Labs introduced a new security feature that gives each chip a unique identifier and does so in a way that’s scalable, making a unique device ID possible”. This is still a work in progress. Silicon Labs’ security vault will be included in its Wireless Gecko Series 2 Platform modules soon.
Preventing insecurity must be our motto.
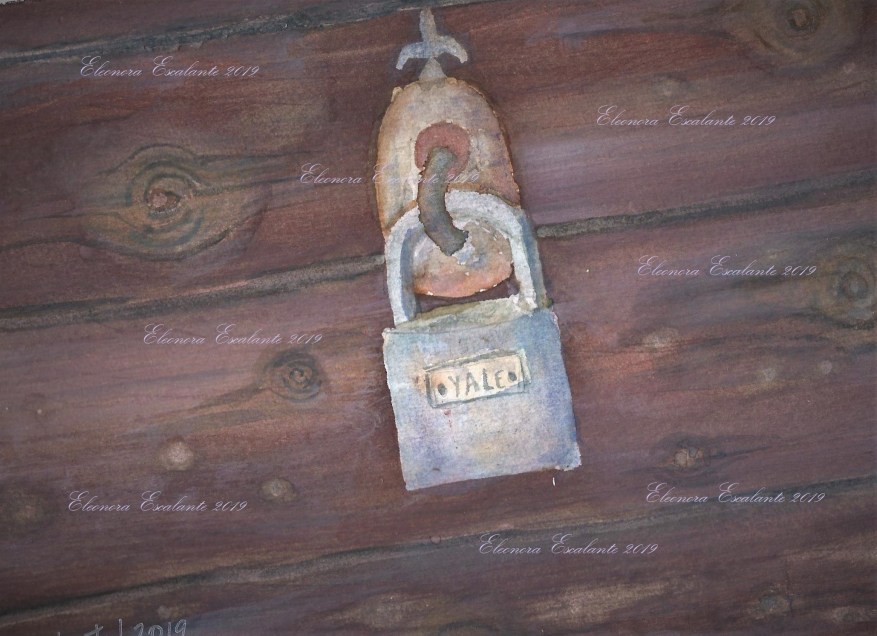
Our life must be protected from any harm. Including the new disruptive technologies damages. A watercolor exercise by Eleonora Escalante. Size: 26 cm x 18 cm. Made with love on watercolor paper Fabriano5 240 GSM Grana Fina.
What is protect?: Protect at its basics is to keep from being damaged, attacked, stolen, injured. Protect is to guard someone, something, “quelque chose”. Protect is to shield, to secure or to defend. Three typical cases of how human beings protect are:
- Parents protect their children from any harm. Normal parents are always defending their children from any type of damage, either physical, emotional, psychological, economical or societal.
- Governments moral proper role is to act justly providing the conditions in which the citizens of the society can interact safely, and prevent gross injury by any individual or group against any other individual or group. In consequence, the top role of governments is to protect citizens, to help them to the extent possible, particularly those who can´t do anything for themselves (the disabled, the extremely poor, the sick, the widows, the orphans and the inwardly ill). Remember that governments’ first obligation is (1) a pursuit of justice to prevent harm and offer security to all ; (2) the second is pursuance for welfare for the needy.
- Private corporations are bound not to harm others. Private ompanies must be moral actors, and their ultimate responsibility falls ultimately on the board of directors. The members of the board of directors are responsible to all stakeholders, choosing the right type of managers and approving its major policies. In consequence the private sector can and should protect the company to be managed honestly and for the well being to the workers, suppliers, competitors and ultimately for its actions to the general public or to society in general. The concept of protection is knead to private corporations too. Private corporations must protect its organizations from:
-
- Whistleblowing,
- Manipulation of the truth and coercion in advertising,
- Trade secrets, amoral disclosure and insider trading
- Manipulation of accounting numbers and financing wrong schemes
- Unfair compensation or wages and Improper worker rights
- Discrimination
- Inequality when it comes to employment and promotions
- Corruption (bribery, unfair outsourcing, slavery, child labor)
- Technology crimes: Wrong use of information, lack of privacy, non-proper cybersecurity systems, excess of technological tools that can harm their employees’ brains and society.
- Internet Insecurity: the private sector must be at the tip-top position when it comes to offering cybersecurity to society.
To be continued… expect the strategic reflection about what we wrote today, on my next publication. Have a beautiful weekend.
Sources of reference utilized today:
https://www.cnet.com/news/favorite-diy-home-security-systems-of-2020-simplisafe-nest-secure/
https://mailchi.mp/iotpodcast/stacey-on-iot-device-fingerprints-for-everyone?e=2416b9ee2e
https://www.aaeon.com/en/ac/safety-and-security
http://vastbright.com/security-systems/
https://www.boschsecurity.com/xl/en/
https://www.safewise.com/best-home-security-system/
https://www.jstor.org/stable/26298674
https://blog.marketresearch.com/8-key-military-applications-for-artificial-intelligence-in-2018
Disclaimer: Illustrations in Watercolor are painted by Eleonora Escalante. Other types of illustrations or videos (which are not mine) are used for educational purposes ONLY. Nevertheless, the majority of the pictures, images or videos shown on this blog are not mine. I do not own any of the lovely photos or images posted unless otherwise stated.
Thank you for reading to me.